Title
Create new category
Edit page index title
Edit category
Edit link
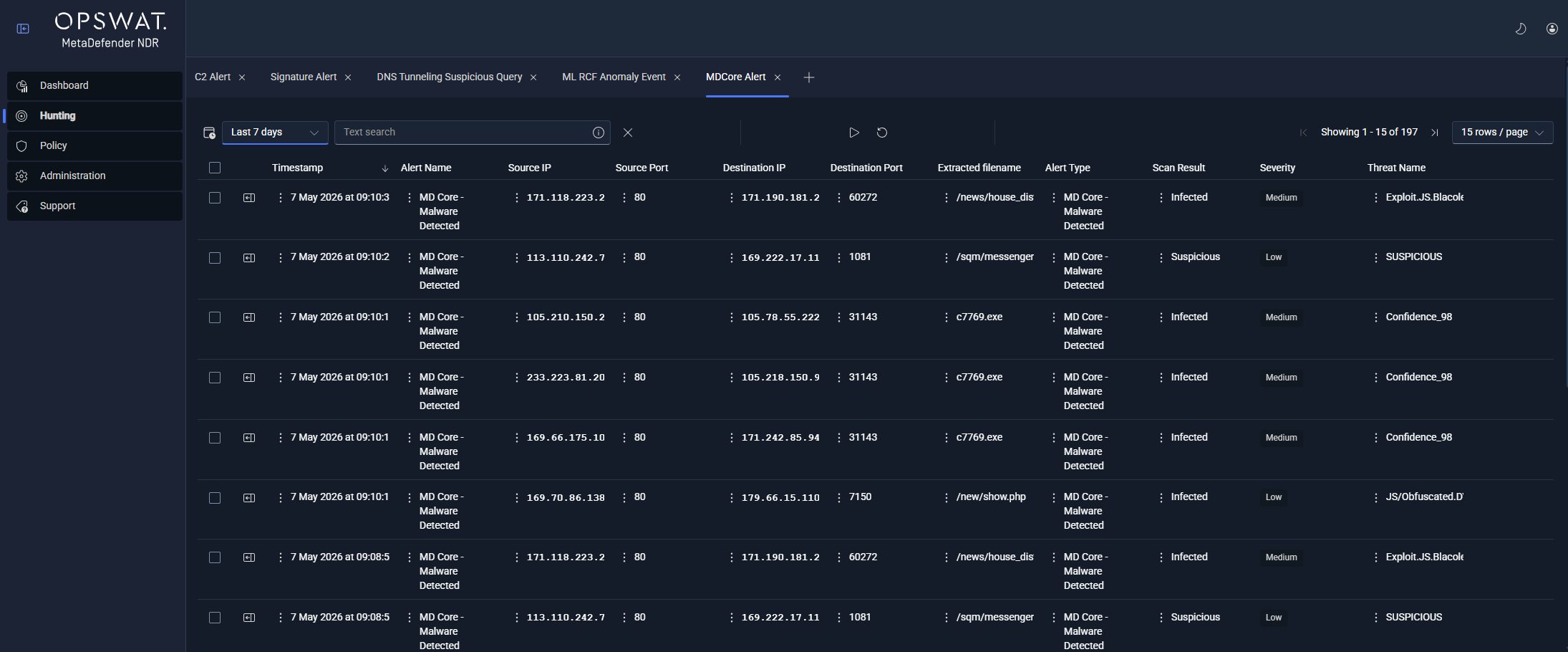
Hunt Page
Overview
The Hunt page answers the question "what happened, who did it, and where else did it show up?" Operators reach the page from the left navigation rail (Hunting) and from the Dashboard Recent Alerts row action, which mounts the Hunt drill-down sidebar in place.
The page is organized around three concepts:
- Event buckets — the top-level groupings into which every event falls. MetaDefender NDR exposes five: All Events, All Alerts, Network Sessions, Netflows, and Files.
- Tabs — a persistent workspace of open investigation views. Each tab is a saved query against a specific bucket and detection type with its own time range, filters, and selection state.
- Detail sidebar — the collapsible pane that opens when an operator selects a row, rendering a full type-specific view of the event with its enrichments and correlations.
A single Hunt session typically carries several tabs open at once: an All Alerts tab for broad triage, a Sessions → DNS tab for a suspected beaconing investigation, a Files tab for recent extractions, and one or more drill-down tabs opened from right-click pivots. Tabs persist across sessions; closing the browser and returning leaves the workspace intact.
Tabs and Tab Lifecycle
Tabs are the organizing unit of the Hunt page. Each tab is a self-contained investigation context: its own query, time window, sort, pagination, and selected row.
Creating a tab
Operators create a tab by picking an entry from the Hunt page menu. The menu is structured by bucket: selecting Alerts → All Alerts opens a new All Alerts tab; selecting Sessions → DNS opens a new DNS session tab. The new tab opens next to the active tab and becomes the focused workspace.
Tabs are also created implicitly by several drill-down actions:
- Clicking the Recent Alerts row action on the Dashboard opens the matching Hunt tab and mounts the sidebar on that row.
- A right-click pivot from a row value (see Right-Click Context Menus on Values, below) opens a new tab pre-filtered to the pivoted value.
- A cross-tab pivot from the sidebar (see Pivoting Between Tabs, below) opens the matching flow, session, or file tab in a new position.
Closing, reordering, and re-opening tabs
Tabs expose a close control on their header. Closing the last tab returns the operator to an empty Hunt surface with the menu ready for a fresh selection. Tabs can be reordered by drag; the order is saved with the workspace.
A closed tab is not recoverable as a tab — closing is destructive — but the same menu entry that originally created it always produces an equivalent blank tab against the same detection type.
Persistence across sessions
The full tab workspace persists per user. That includes, for each tab: its bucket and detection type, the applied time range, quick-search text, column width and order customizations, pagination, and the currently selected row (if any). Returning to the Hunt page after signing out and back in restores the workspace.
User-level persistence is scoped by event bucket so that column preferences carried across, say, DNS session tabs do not interfere with column preferences on Network Session tabs.
Tab Types
Every tab is rooted in one of five event buckets. Selecting a bucket with no sub-type opens a unified view; selecting a sub-type opens a tab with the column projection and sidebar renderer specific to that type.
All Events
The widest view. All Events returns every event regardless of type — alerts, sessions, flows, and files — with the minimum common column set (timestamp, protocol, source and destination endpoints). Operators use it as a triage starting point when they do not yet know what kind of event triggered the behavior they are hunting.
All Alerts (Alert Pipeline)
All Alerts returns every record that reached the alerting pipeline: Suricata signature alerts, C2 and Threat Intelligence (InSights) alerts, MetaDefender Core alerts, behavioral detections, and ML anomaly alerts. The common column set is timestamp, protocol, source and destination endpoints, alert type, and severity.
Per-type sub-tabs narrow All Alerts to a single detection family:
Every alert sub-tab exposes severity (Critical, High, Medium, Low) as a first-class column and supports the same right-click pivots described below.
| Sub-tab | What it Contains |
|---|---|
| SignatureAlert | Classic intrusion-detection signature hits from Suricata with signature message, identifier (SID), category, MITRE technique and tactic, and payload. |
| C2 Infrastructure Alert | Matches against command-and-control (C2) IP and domain threat intelligence, with match type, matched value, score, confidence, and source feed. |
| InSights Alert | Matches against OPSWAT InSights Threat Intelligence Database (TIDB) and Reputation Database (REPDB), with the matched entity and source tagging. |
| MDCore Alert | MetaDefender Core file-scan verdicts: scan result, threat name, detection engine coverage, and file metadata. |
| Behavioral detections (one sub-tab per type) | Beaconing, Data Exfiltration, Long Duration, DNS Tunneling, DGA, Fast Flux, Port Scan, Connection Spray, and the Composite / Unified aggregates. See [Behavioral detections_](_Behavioral detections) for the full catalog. |
| ML Random Cut Forest Anomaly | Anomaly detections from the RCF model, carrying the anomaly score, the threshold the score crossed, the model version, and the underlying event that scored. |
Network Sessions
Network Sessions returns per-protocol session records — one row per protocol transaction — in a unified table. Per-protocol sub-tabs apply a projection specific to each protocol parser:
| Sub-tab | Protocol-specific fields |
|---|---|
| DNS | Query name, record type, response code, TTL, answer data. |
| HTTP | Hostname, URL, method, status, user agent, referer, content-type, response length |
| TLS | Version, SNI, certificate subject and issuer, validity window, JA3 / JA3S / JA4 fingerprints, cipher, session resumption flag. |
| QUIC | Version, SNI, JA3 / JA4 fingerprints, client / server Application-Layer Protocol Negotiation (ALPN). |
| SSH | Protocol version, client and server software, HASSH client and server fingerprints, key-exchange and cipher algorithms. |
| SMB | Command, filename, share, access flags, status. |
| RDP | Client name, client build, cookie, keyboard layout, X.509 certificate subject and issuer. |
| SMTP | Mail-from, recipients, HELO, attachment filenames, reply codes. |
| FTP | Command, command data, reply code. |
| FileInfo | Filename, magic string, SHA-256, Message Digest 5 (MD5), size, state, stored flag. See Files below. |
Every session row carries the standard 5-tuple (source IP and port, destination IP and port, protocol) and a community_id correlator that joins all events belonging to the same connection. When the sensor and enrichment pipeline have attached intelligence to an entity on the row — for example, a TIDB match on the DNS query name — the relevant enrichment ribbon appears inline and the full enrichment payload is available in the sidebar.
Operational Technology (OT) protocol event types (Modbus, DNP3, Ethernet/Internet Protocol (ENIP) / Common Industrial Protocol (CIP), S7comm, Building Automation and Control Networks (BACnet), IEC 60870-5-104 (IEC104)) are on the roadmap and will appear as additional Network Sessions sub-tabs when they ship.
Netflows
Netflows returns NetFlow and connection-summary records — one row per flow, emitted after flow timeout or protocol-parser close. Columns include packets and bytes per direction (to-server and to-client), flow start, end, and age, flow state, termination reason, alerted flag, transaction count, and exception policy.
Netflows is the primary surface for packet-and-byte-volume investigations: which internal host uploaded 2 gigabytes to which external IP over what window, which long-duration connections remain open, and which connections were terminated abnormally.
Files
Files returns FileInfo events — one row per file the sensor extracted from observed traffic. Columns include filename, magic string, SHA-256, MD5, file size, state (CLOSED when the file is eligible for MetaDefender Core enrichment), and stored flag.
When MetaDefender Core enrichment is enabled and the file has been scanned, the row also carries the scan result and threat name. A right-click pivot on the SHA-256 column opens an All Events tab showing every event that referenced the same file hash (HTTP download, SMB write, SMTP attachment) so the analyst can trace the file's path across the network.
Search and Filtering
The top bar of every Hunt tab exposes three controls that govern what the table returns: quick search, the time selector, and the advanced-search query builder.
Quick search
Quick search is a single text box in the top bar that applies a free-text search across the event's key indexed fields. Operators use it for fast entity lookups — a suspected malicious domain, a specific IP, a SHA-256 hash, a signature name — without opening the advanced builder.
The set of fields covered by quick search is intentionally narrow so the query stays fast on high-volume deployments; operators who need to match against a field outside that set use the advanced search builder instead.
Time selection
Time selection is a dual-mode control that combines a relative picker (for example, Last 15 minutes, Last 1 hour, Last 24 hours, Last 7 days) with a calendar range picker (for example, June 12 09:00 – June 12 17:00). Operators toggle between the two modes without losing the in-progress selection.
The selected time range applies to every query the tab issues and is persisted per tab. Very wide ranges (Last 7 days, Last 30 days, custom multi-week ranges) increase query latency; operators narrow the range when they need responsive iteration and widen it only to confirm long-tail behavior.
Advanced search
Advanced search is a visual query builder accessed from the top bar. It supports the full Boolean grammar — AND, OR, NOT — combined with field-specific filters that project the correct operator for each field type (equality for categorical fields, prefix for hostnames, range for numeric fields, set membership for enumerations). Expressions can be nested to build arbitrarily complex conditions.
The advanced-search payload is held with the tab; switching tabs does not clear the builder state, and returning to the tab later restores the last-applied expression. Saved named searches are not part of MVP — operators recreate complex queries by re-opening them from the tab workspace.
Faceting and column filtering
Column filtering on the results table (per-column filter inputs rendered in the table header) is on the roadmap. On MVP, operators narrow results by composing the query in advanced search or by pivoting from a row value in the existing result set.
Real-time mode
Every tab has a real-time mode that continuously refreshes the result set as new events land in storage. In real-time mode the table repolls at a short cadence and new rows appear at the top; end-to-end latency from sensor observation to the Hunt table is under ten seconds under normal conditions.
Operators switch a tab between real-time and historical mode from a toggle in the top bar. Historical mode runs a single query against the selected time range and holds the result set stable for investigation. True push-based streaming with configurable auto-scroll is tracked on the roadmap; MVP real-time mode is poll-based continuous refresh.
Sort and Pagination
Every column in the results table is sortable. Clicking a column header toggles ascending, descending, and cleared states; the active sort is indicated by an arrow glyph on the header.
Pagination is controlled from the table footer. Operators choose the rows-per-page count from a fixed set:
- 10
- 25
- 50
- 100
- 250
- 500
Page navigation (first, previous, next, last, and direct page entry) is on the same footer. Sort and pagination state persist with the tab.
Column widths can be resized by dragging the header divider, and columns can be reordered by dragging the header. Both are saved per user and per event bucket, so column preferences applied to, for example, the DNS sub-tab carry across other DNS sub-tabs.
Show / hide column controls (choosing which of the available fields render as columns) are tracked on the roadmap. On MVP, the column set is the bucket- and sub-type-specific projection documented in Tab Types above.
Working with Results
A row is the atomic unit the operator acts on.
- Select a row. Clicking a row opens the detail sidebar on the right (see The Detail Sidebar, below). A single row is selected at a time.
- Copy a value. Right-clicking a cell exposes Copy in the context menu (see Right-Click Context Menus on Values, below).
- Pivot from a value. Right-clicking a cell also exposes the pivot actions — Hunt all events from this IP, Show related events, Show related files, Search file hash across all events, Show all events with this community id — each of which opens a new tab pre-filtered to the selected value.
- Export the result set. The tab exports to Comma-Separated Values (CSV) or JavaScript Object Notation (JSON) from the tab action menu. Export respects the active search, filters, time range, and sort; the row cap on export matches the platform limit documented in (Link Removed)
Multi-row selection and bulk actions — assigning rows to an analyst, tagging rows, dispositioning rows — are not part of MVP. Operators who need to route events to downstream systems use the Security Information and Event Management (SIEM) and syslog integrations described under (Link Removed)
The Detail Sidebar
The detail sidebar is the collapsible pane that opens on the right side of the page when an operator selects a row. It renders the full event with every available field laid out in sections specific to the event type, plus any enrichments attached by the pipeline.
Carousel multi-event navigation
The sidebar header exposes next / previous controls that step through the currently-visible result page without closing the sidebar. Operators use the controls to walk a page of alerts end-to-end without returning to the table between rows. Stepping past the end of the current page advances to the first row of the next page; stepping backward past the first row returns to the last row of the previous page.
Type-specific renderers
The sidebar dispatches a different renderer based on which event blocks are present on the record. One record can fire several renderers at once — for example, a DNS session row that matched a TIDB entry renders the DNS section alongside the InSights Enrichment section, and a FileInfo row with a MetaDefender Core hit renders the FileInfo section alongside the MDCore Enrichment section.
The renderers shipped on MVP:
| Event Type | Sidebar Section | What it shows |
|---|---|---|
| Signature Alert | Suricata Alert + Payload | Signature message, SID, revision, category, severity, action, MITRE technique and tactic, affected product, attack target, malware family, author, confidence, rule metadata, plus the base64 and printable payload. |
| DNS Event | Suricata DNS | Query name, record type, response code, answer data, TTL, query-or-answer flag. |
| HTTP Event | Suricata HTTP | Hostname, URL, method, status, response length, user agent, referer, content-type, request and response headers. |
| TLS Event | Suricata TLS | Version, SNI, subject, issuer, serial, fingerprint, JA3 / JA3S / JA4 fingerprints, cipher, validity window, session-resumed flag. |
| SSH Event | SSH detail (generic ontology-driven block) | Protocol version, client and server software, HASSH fingerprints, key exchange and cipher algorithms. |
| SMB Event | SMB detail (generic ontology-driven block) | Command, share, filename, access flags, status. |
| RDP Event | RDP detail (generic ontology-driven block) | Client name, client build, cookie, version, certificate subject and issuer. |
| SMTP Event | SMTP detail (generic ontology-driven block) | Mail-from, recipients, HELO, attachment filenames, reply codes. |
| QUIC Event | Suricata QUIC | Version, SNI, JA3 / JA4 fingerprints, ALPN. |
| FTP Event | FTP detail (generic ontology-driven block) | Command, command data, reply code. |
| FileInfo Event | Suricata FileInfo | Filename, magic string, SHA-256, MD5, file size, state, stored flag. |
| Flow Event | Suricata Flow | Packets to-server and to-client, bytes to-server and to-client, start, end, age, state, termination reason, alerted flag, transaction count, exception policy. |
| MD Core Enrichment Section | MD Core | Scan result, threat name, positive engines over total engines, scan details per antivirus engine, cache-hit flag, file metadata (SHA-256, MD5, size, type). |
| C2 Enrichment Section | C2 Infrastructure | Match type, matched value, confidence, score, source feed — one block per C2-matched entity on the row. |
| InSights Enrichment Section | InSights | Malicious flag, source tagging, matched entity — one block per InSights-matched entity on the row. |
| Behavioral Alert Sections | One section per detection nested key (Beaconing, Data Exfiltration, Long Duration, DNS Tunneling, DGA, Fast Flux, Port Scan, Connection Spray, and the composite aggregates) | Detection-specific metadata: connection counts, byte ratios, upload / download totals, window bounds, destination country / Autonomous System Number (ASN) / organization, malicious Indicators of Compromise (IOC) lists. |
Clicking the sidebar close control returns the full table width; re-opening a row in the same tab re-mounts the sidebar on the new row.
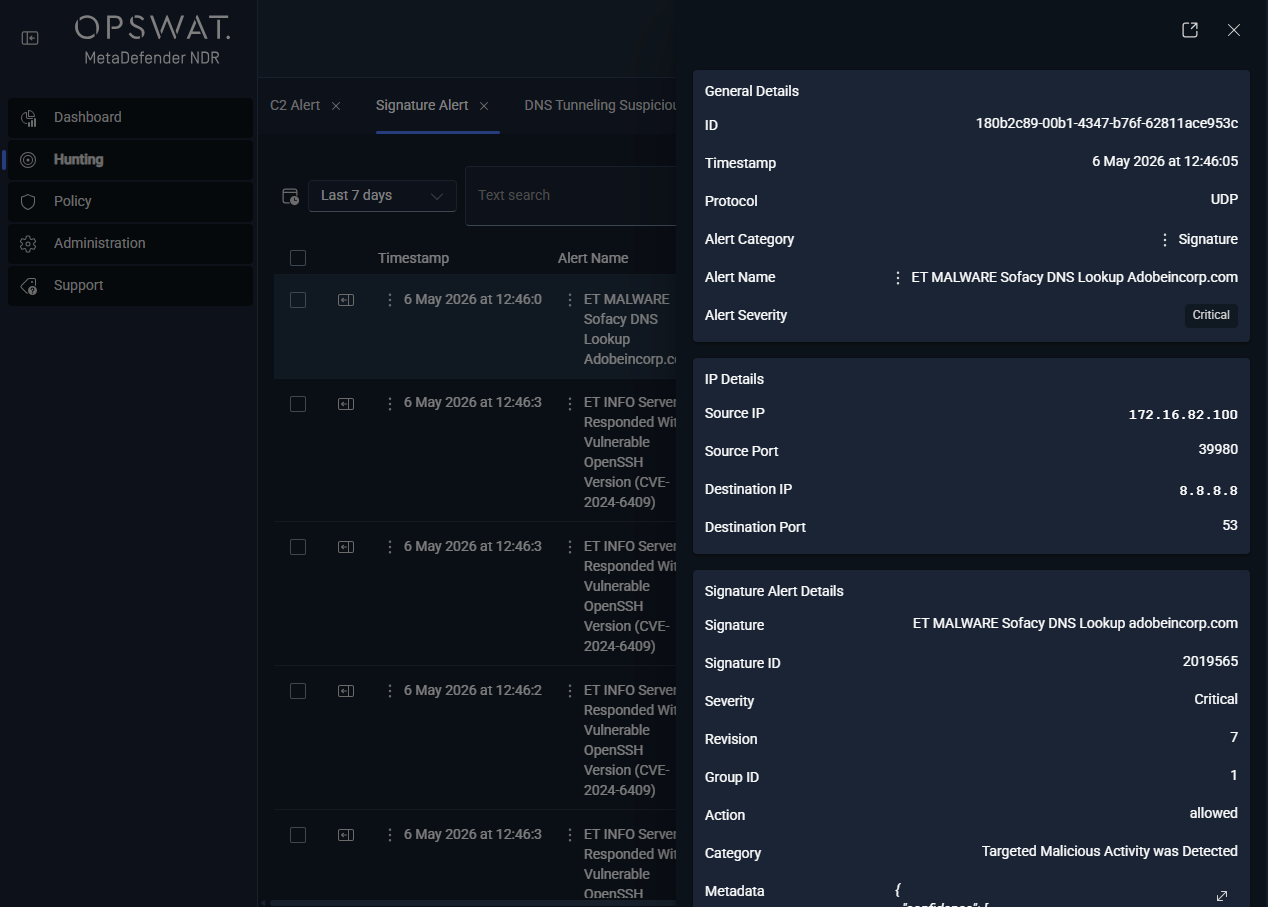
Right-Click Context Menus on Values
Every cell value in the results table and every field value in the sidebar exposes a right-click context menu. The menu carries two classes of action: copy and pivot.
Right-click pivots always open a new tab; the originating tab is preserved so the operator can walk back after following a lead.
| Action | Scope | What happens |
|---|---|---|
| Copy to clipboard | Any cell or sidebar field value | The selected value is placed on the system clipboard. |
| Hunt all events from this IP | Any IP-valued cell (source or destination) | A new tab opens on All Events filtered to rows where the IP appears in either the source or destination 5-tuple position. The selected time range carries over from the originating tab. |
| Show related files | Any row with a flow or session context | A new tab opens on the Files bucket filtered to files observed on the same flow — useful for seeing what file was transferred across a suspicious connection. |
| Show related events | Any row | A new tab opens on All Events filtered to events that share the row's community_id — that is, every event belonging to the same connection. |
| Search file hash across all events | Any file hash cell (SHA-256 or MD5) | A new tab opens on All Events filtered to events that reference the hash, including the upstream HTTP download, the SMB write, and the downstream MDCore scan. |
| Show all events with this community id | Any row with a community_id | A new tab opens on All Events filtered to that community_id — the connection-level view of every protocol transaction and enrichment on the same 5-tuple session. |
Pivoting Between Tabs
Pivoting is the core investigative motion on the Hunt page: following an indicator from one view into another with the filter set carried over.
Three pivots happen commonly:
- Alert → flow. An operator studying an All Alerts row right-clicks the
community_idand selects Show all events with this community id. A new All Events tab opens with every protocol transaction, every flow record, every file extraction, and every enrichment attached to that connection. - Flow → session. An operator studying a long-duration flow on Netflows right-clicks the
community_idand selects Show related events. The resulting tab exposes the DNS resolution, TLS handshake, and HTTP requests that happened on that flow. - Session → file. An operator studying an HTTP session right-clicks the row and selects Show related files. The resulting Files tab lists every file extracted from the same flow, with MetaDefender Core scan results where available.
The same pivots run from the sidebar. Right-clicking a value inside the sidebar — an IP in the flow section, a hash in the fileinfo section, a community_id header — exposes the same pivot menu as the table row, so analysts investigating from the sidebar do not have to return to the table to follow the indicator.
Roadmap additions (see Roadmap, below) include a dedicated correlation view that surfaces related events without requiring an explicit pivot, and a file-to-endpoint tracing view that visualizes the source → file hash → destination endpoints relationship directly.
Saving Hunt Context
MetaDefender NDR preserves Hunt context through the tab persistence model rather than through a dedicated saved-query UI.
What persists
Every tab is saved to the user's workspace. For each tab the platform persists:
- The bucket and detection type (which menu entry created it).
- The selected time range.
- The active quick-search text and advanced-search expression.
- Column width and order customizations (scoped per event bucket).
- Sort state and rows-per-page selection.
- The page position.
Signing out and back in — from the same browser or a different one — restores every open tab to the last-saved state.
What does not persist
Row selection and sidebar-open state are transient and reset at sign-in. Operators who need to return to a specific row bookmark it by leaving the tab open, rather than by saving the row directly.
Sharing a Hunt context
A named save / load / share workflow for complex queries — so an analyst can hand a query to a peer, an incident responder can capture the filter that scoped an investigation, or a runbook can reference a specific Hunt view by name — is on the roadmap. On MVP, analysts reproduce a peer's context by applying the same menu selection, time range, and advanced-search expression manually, and they reference Hunt views from incident documentation by describing the applied filters rather than by a stable identifier.
See Also
- Dashboard— the overview surface that feeds Hunt via the Recent Alerts row action.
- Detection Overview — the catalog of detection families whose alerts land in All Alerts and its per-type sub-tabs.
- Critical Alert Triage— the runbook that uses the Hunt page end-to-end for first-response triage.
- Alert, Flow, and PCAP Pivoting — extended coverage of the pivot patterns introduced in this chapter.
- (Link Removed) — the severity label definitions used in the alert columns.