Title
Create new category
Edit page index title
Edit category
Edit link
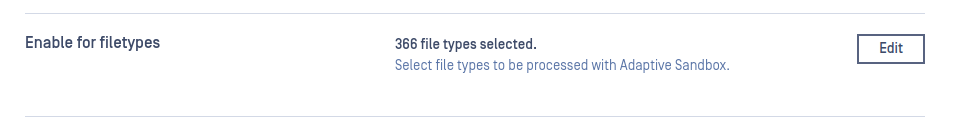
Embedded Engine
The required Java for the embedded Sandbox is Java 17. While Java 8 or 11 may still function temporarily, they will no longer work at all after March 2025. Please plan to upgrade to Java 17 before March 2025 to avoid any disruption
The default system Java version should be set correctly; please check if the correct version is used. The computer should be restarted after Java installation. Upgrade to Java 17
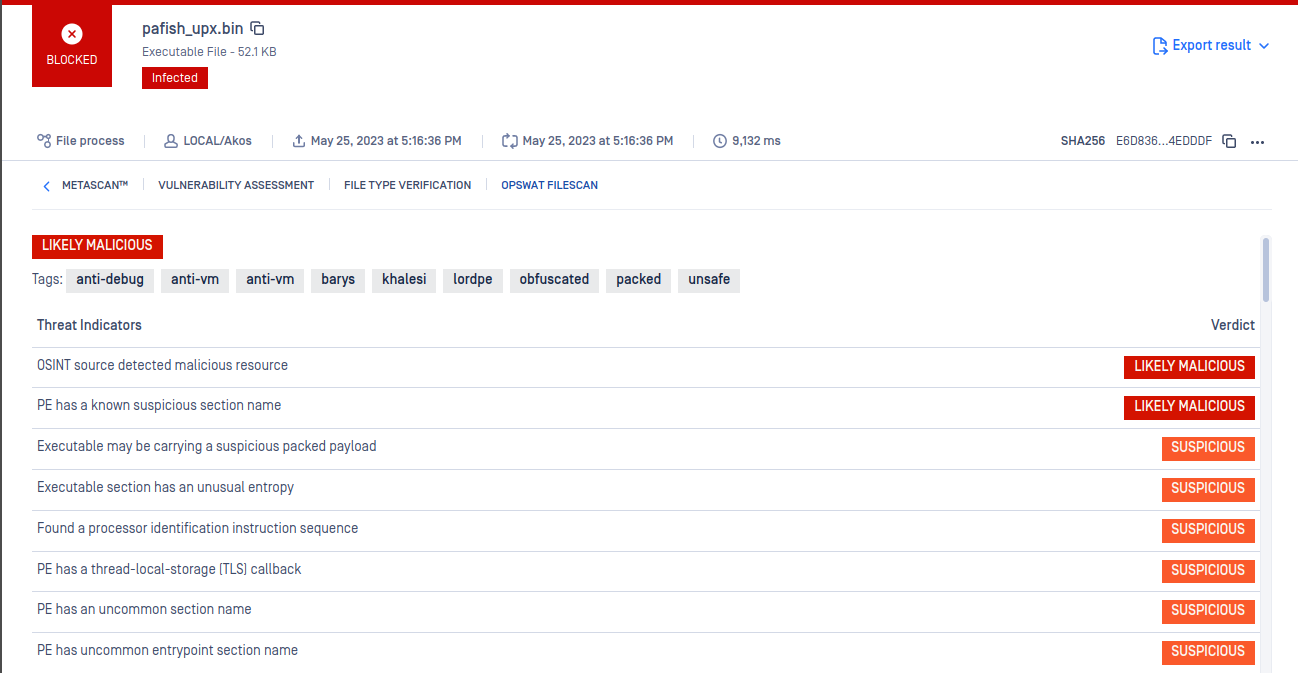
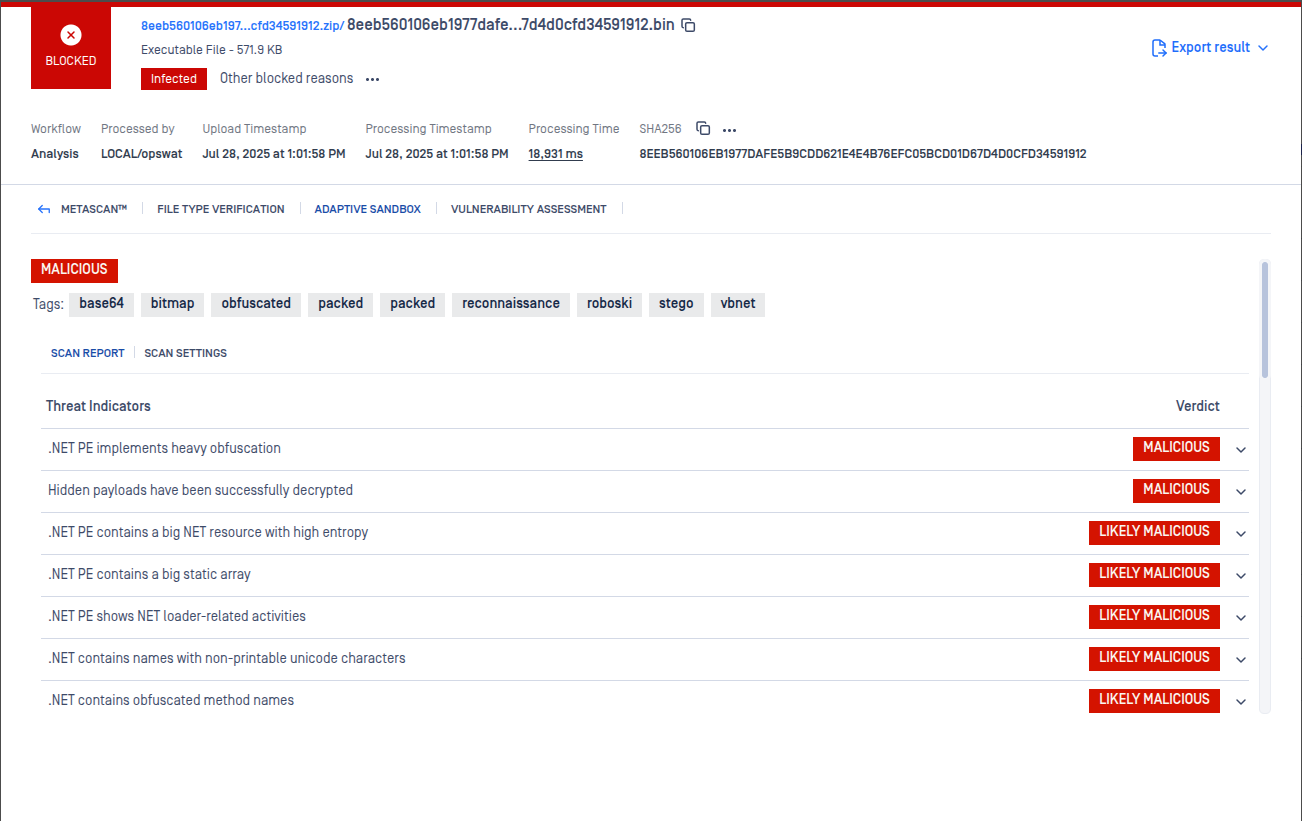
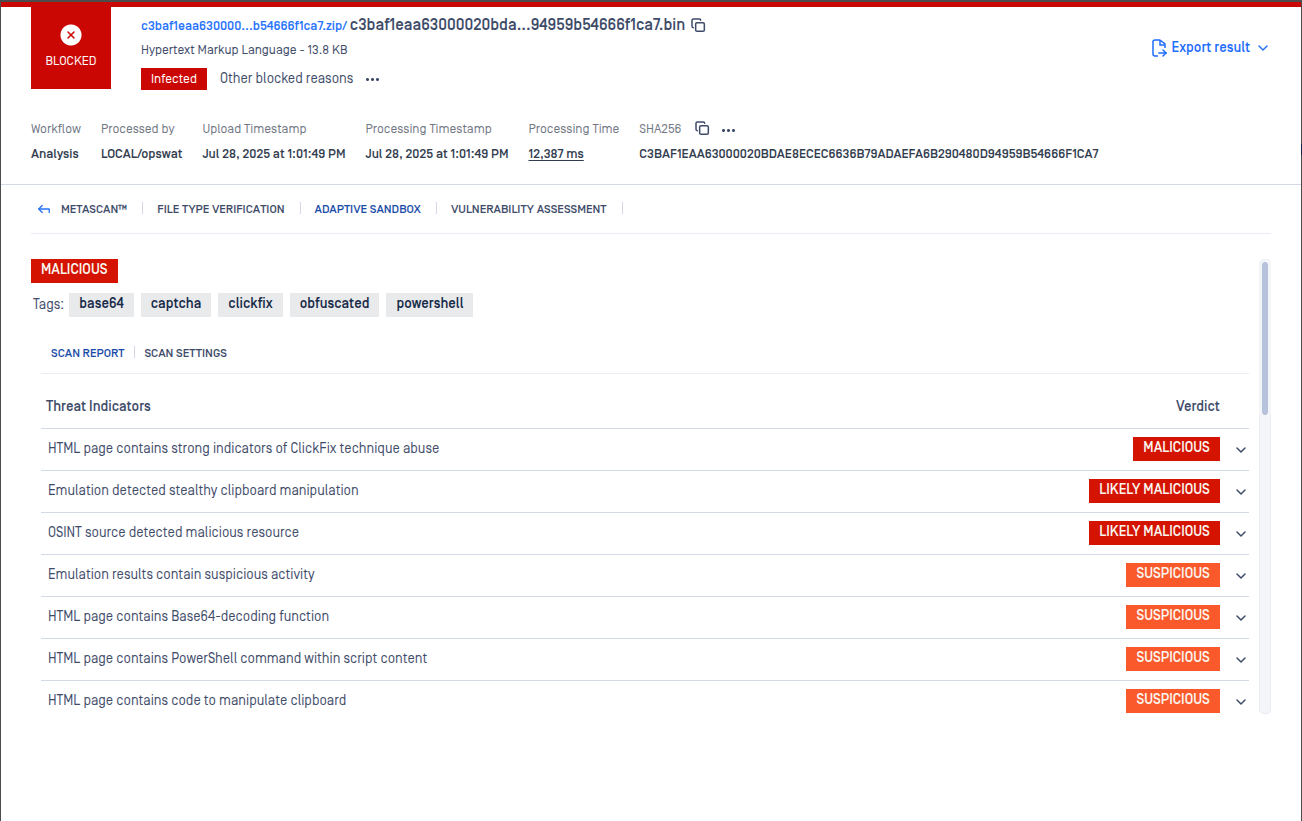
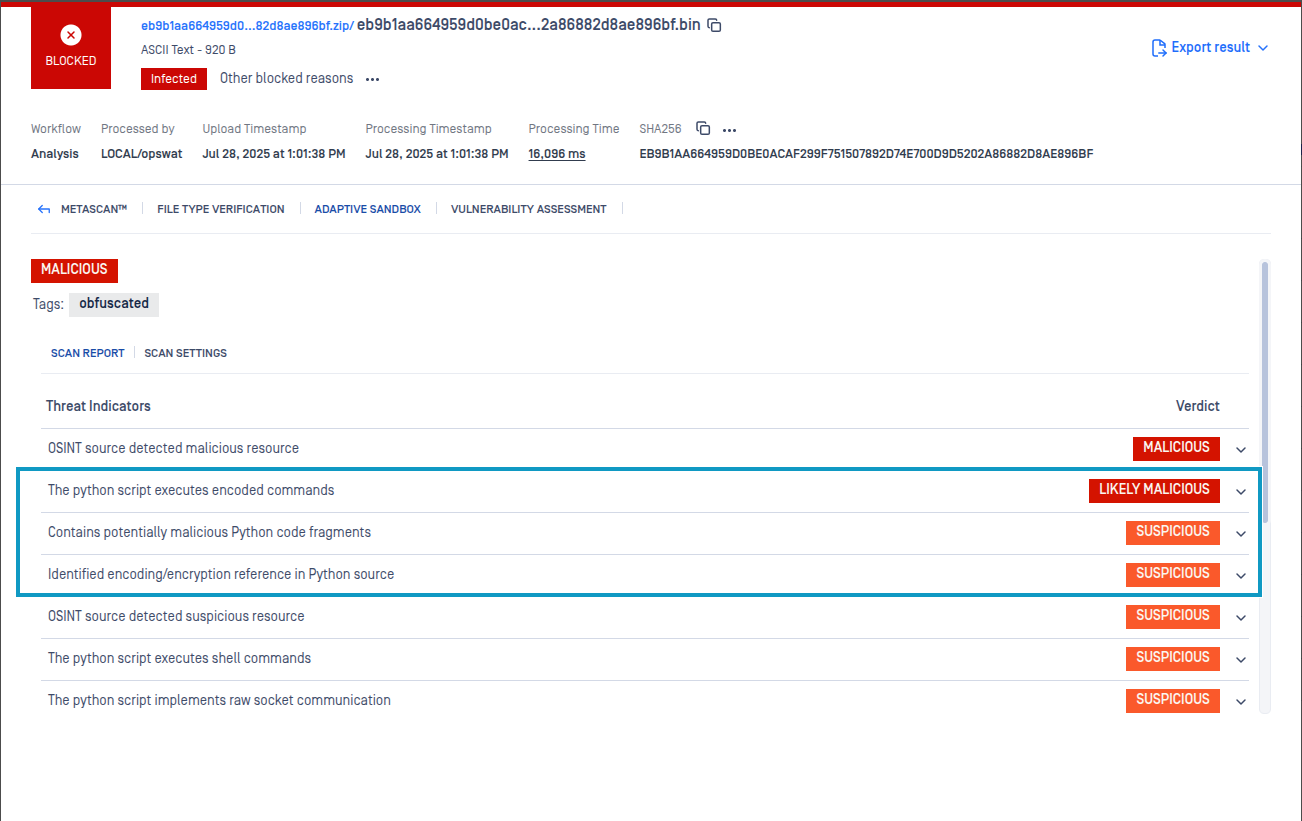
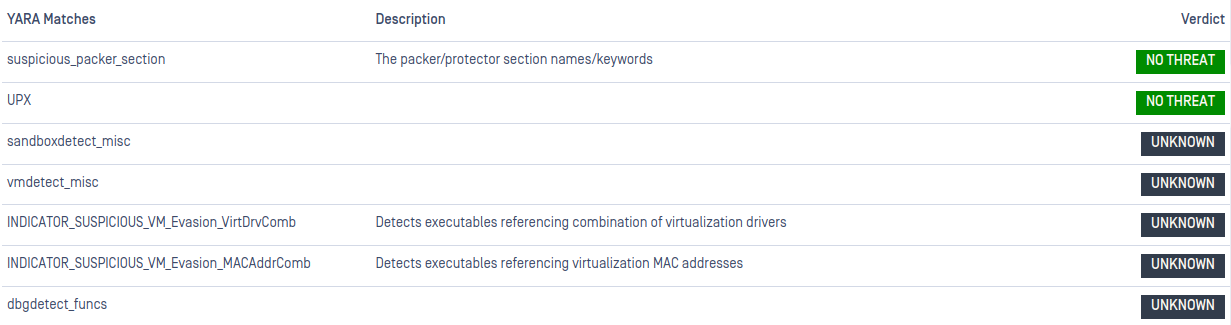
This release artifact contains False Positive files (pycdc, upx, nuitka-extractor) that are incorrectly detected by the Cylance and Quick Heal AV engines. If you are scanning the release artifact with MetaDefender Core, please enable the Reputation engine as explained here to avoid these misdetections: https://www.opswat.com/docs/mdcore/reputation-engine/configuration-reputation-engine
Known issues
| Issue | Solution |
|---|---|
| MSI certificate validation is not supported on Windows OS | - |
v2.4.0
Release date: 07/31/2025
| New Features and Improvements |
|---|
What's New
Improvements
Bug Fixes
|
v2.3.0
Release date: 06/05/2025
| New Features and Improvements |
|---|
|
v2.2.0
Release date: 02/17/2025
| New Features and Improvements |
|---|
|
v2.1.0
Release date: 12/02/2024
| New Features and Improvements |
|---|
|
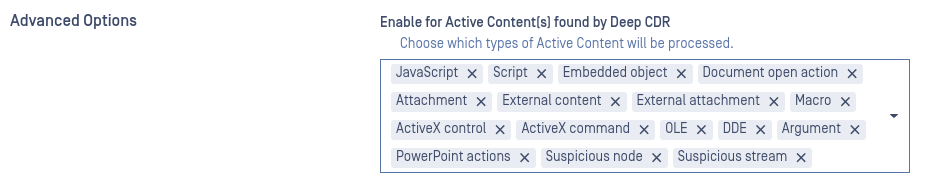
Deep CDR Triggers
v2.0.0
Release date: 08/28/2024
| New Features and Improvements |
|---|
Fixes and improvements:
|
v1.7.1
Release date: 05/24/2024
| New Features and Improvements |
|---|
|
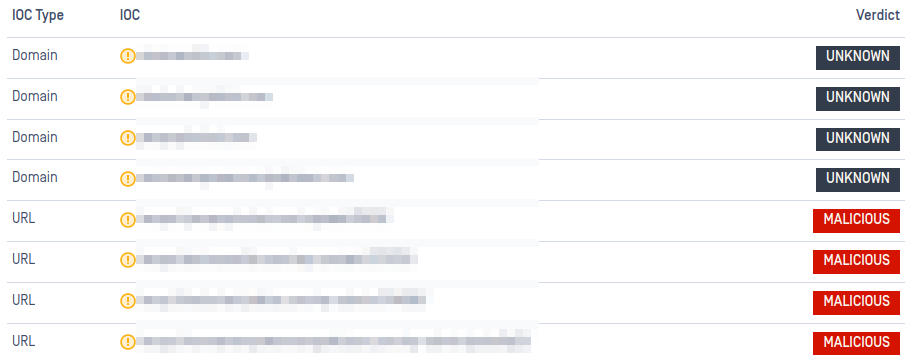
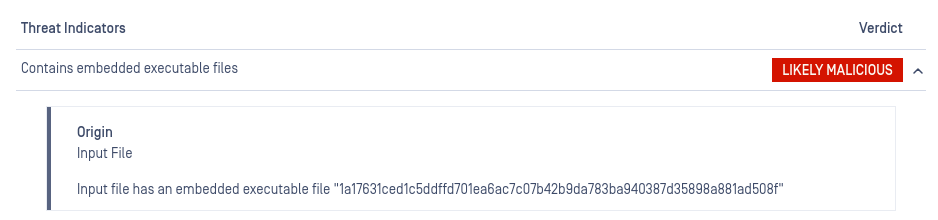
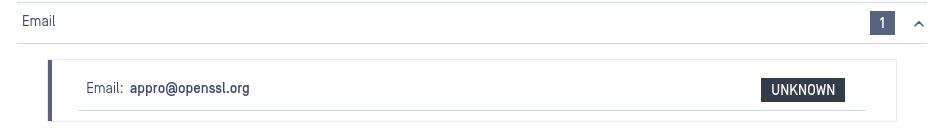
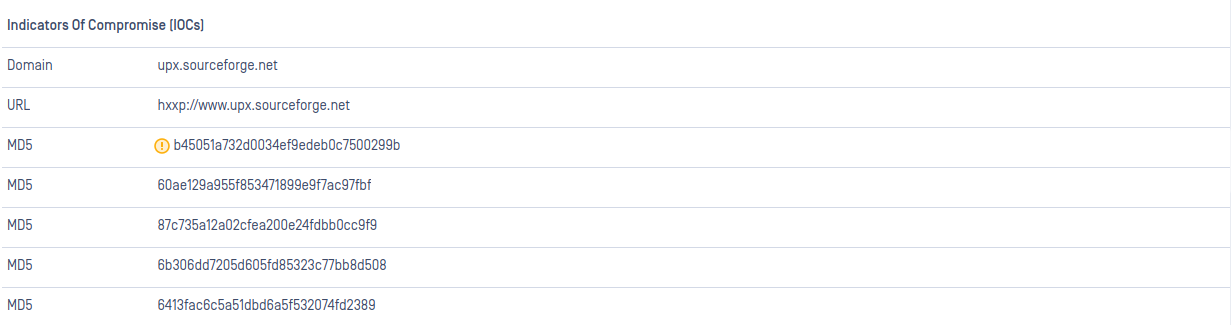
Verdict for IOCs
v1.7.0
Release date: 04/26/2024
| New Features and Improvements |
|---|
|
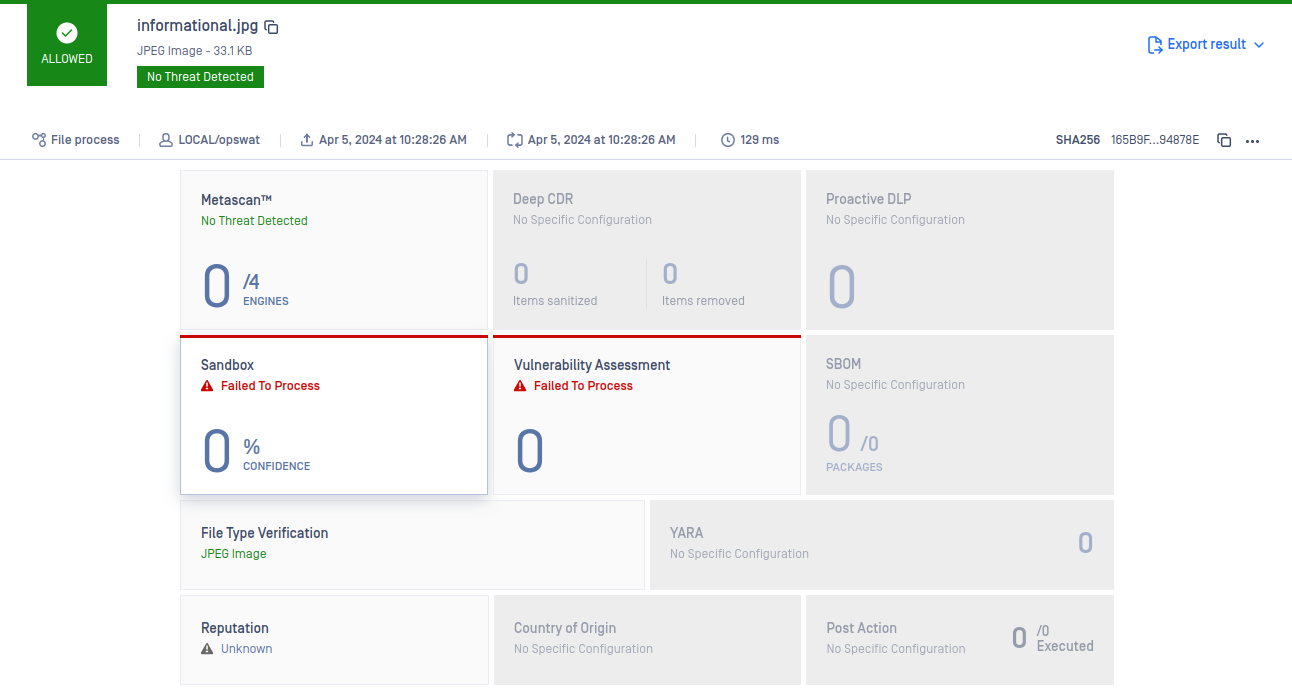
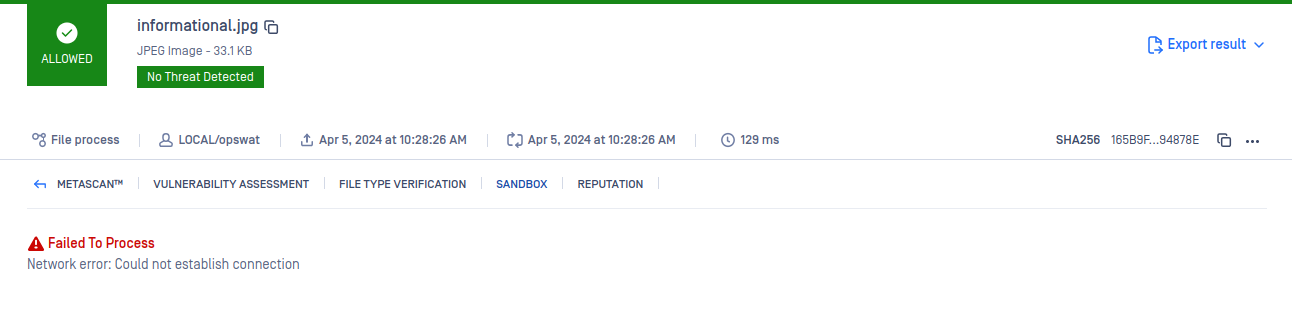
Improved error reporting
v1.6.0
Release date: 01/29/2024
| New Features and Improvements |
|---|
|
v1.5.0
Release date: 11/06/2023
| New Features and Improvements |
|---|
|
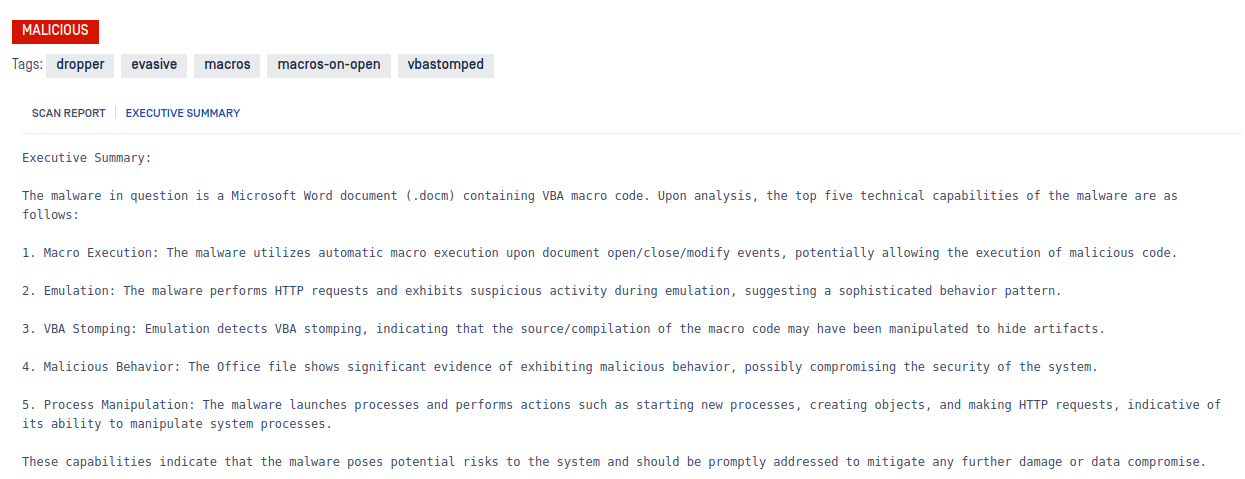
Executive Summary

Crypto Wallets
| Known issues |
|---|
|
v1.4.0
Release date: 09/22/2023
| New Features and Improvements |
|---|
|
v1.3.4
Release date: 08/02/2023
| New Features and Improvements |
|---|
|
v1.3.3
Release date: 07/07/2023
| New Features and Improvements |
|---|
|
v1.3.2
Release date: 06/14/2023
| New Features and Improvements |
|---|
|
v1.3.1
Release date: 06/05/2023
| New Features and Improvements |
|---|
|
v1.3.0
Release date: 05/26/2023
| New Features and Improvements |
|---|
|
v1.2.0
Release date: 05/17/2023
| New Features and Improvements |
|---|
|
v1.1.0
Release date: 05/08/2023
| New Features and Improvements | |
|---|---|
|
v1.0.0
Release date: 04/06/2023
| New Features and Improvements |
|---|
|